Let's take a deeper look at the Q1 2023 DDoS attacks mitigation statistics and observations from Qrator Labs' perspective.
The Qrator Labs company has temporarily suspended it’s blog on Habr

Let's take a deeper look at the Q1 2023 DDoS attacks mitigation statistics and observations from Qrator Labs' perspective.
Now that 2022 has come to an end, we would like to share the DDoS attack mitigation and BGP incident statistics for the fourth quarter of the year, which overall saw unprecedented levels of DDoS attack activity across all business sectors.
In 2022, DDoS attacks increased by 73.09% compared to 2021.
Let's take a closer look at the Q4 2022 data.
All the credit is due to the RFC’s authors: A. Azimov (Qrator Labs & Yandex), E. Bogomazov (Qrator Labs), R. Bush (IIJ & Arrcus), K. Patel (Arrcus), K. Sriram.
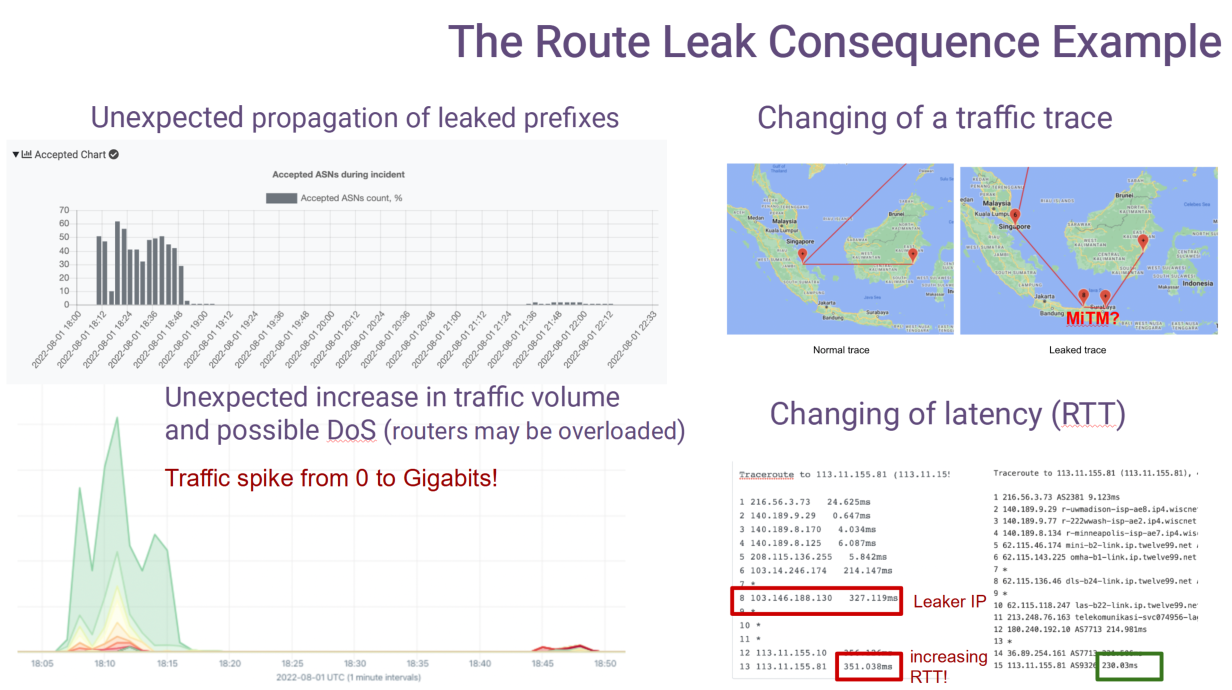
A BGP route leak is an unintentional propagation of BGP prefixes beyond the intended scope that could result in a redirection of traffic through an unintended path that may enable eavesdropping or traffic analysis, and may or may not result in an overload or complete drop (black hole) of the traffic. Route leaks can be accidental or malicious but most often arise from accidental misconfigurations.

With the end of the 2022' third quarter, we invite you to take a tour into DDoS attacks mitigation and BGP incidents statistics recorded from July to September.

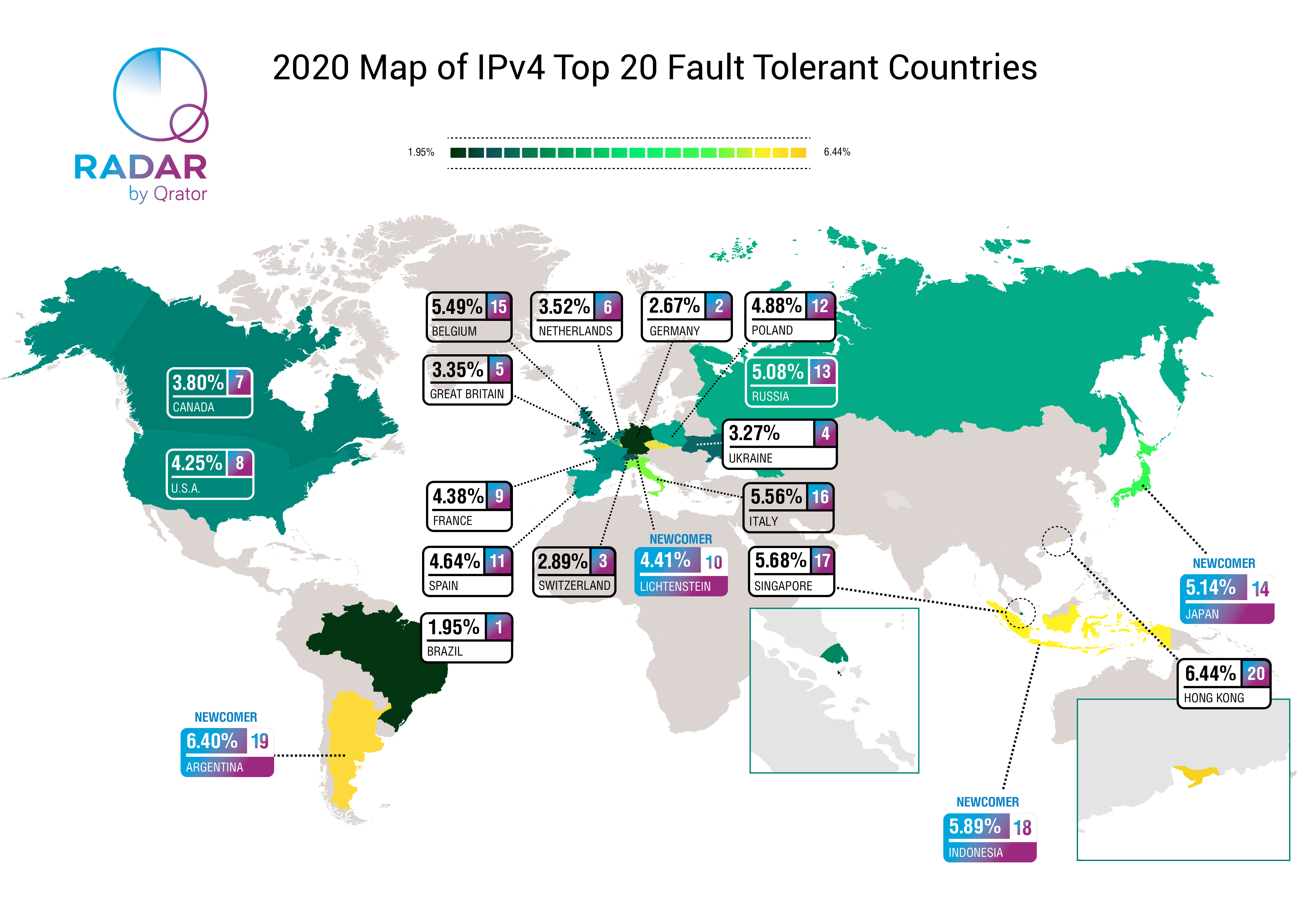
The National Internet Segment Reliability Research explains how the outage of a single Autonomous System might affect the connectivity of the impacted region with the rest of the world. Generally, the most critical AS in the region is the dominant ISP on the market, but not always.
As the number of alternate routes between ASes increases (the "Internet" stands for "interconnected networks" - and each network is an AS), so does the fault-tolerance and stability of the Internet across the globe. Although some paths are more important than others from the beginning, establishing as many alternate routes as possible is the only viable way to ensure an adequately robust network.
The global connectivity of any given AS, whether an international giant or a regional player, depends on the quantity and quality of its path to Tier-1 ISPs.
Usually, Tier-1 implies an international company offering global IP transit service over connections with other Tier-1 providers. Nevertheless, there is no guarantee that such connectivity will always be maintained. For many ISPs at all "tiers", losing connection to even one Tier-1 peer would likely render them unreachable from some parts of the world.
The second quarter of the year has ended and, as usual, we take a look back at the mitigated DDoS attacks activity and BGP incidents that occurred between April and June 2022.
The first quarter of the year 2022 has passed; now, it is time to look at the events of Q1 in terms of mitigated DDoS activity and recorded BGP incidents.
2021 was an action-packed year for Qrator Labs.
It started with the official celebration of our tenth year anniversary, continued with massive routing incidents, and ended with the infamous Meris botnet we reported back in September.
Now it is time to look at the events of the last quarter of 2021. There are interesting details in the BGP section, like the new records in route leaks and hijacking ASes, but first things first, as we start with the DDoS attacks statistics.
DDoS attacks send ripples on the ocean of the Internet, produced by creations of various sizes - botnets. Some of them feed at the top of the ocean, but there also exists a category of huge, deep water monstrosities that are rare and dangerous enough they could be seen only once in a very long time.
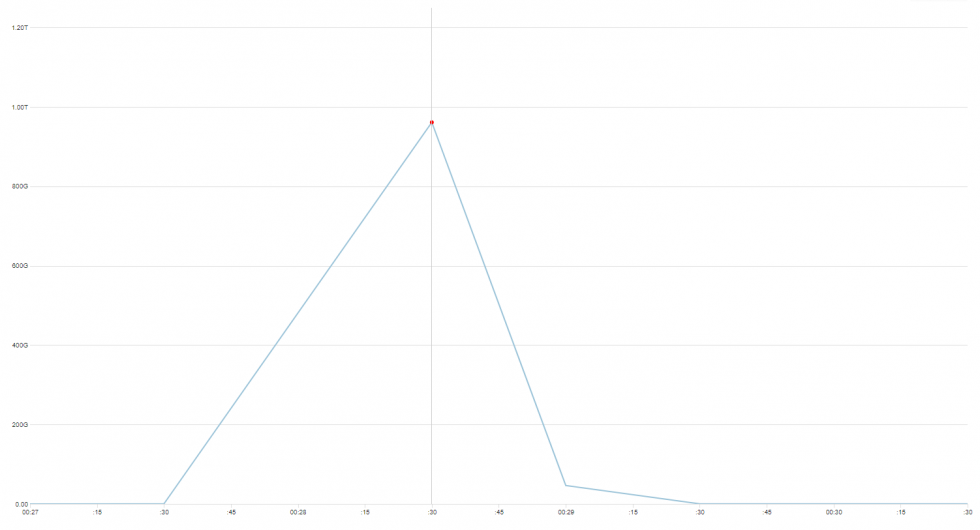
November 2021 we encountered, and mitigated, several attacks from a botnet, that seems to be unrelated to one described and/or well-known, like variants of Mirai, Bashlite, Hajime or Brickerbot.
Although our findings are reminiscent of Mirai, we suppose this botnet is not based purely on propagating Linux malware, but a combination of brute forcing and exploiting already patched CVEs in unpatched devices to grow the size of it. Either way, to confirm how exactly this botnet operates, we need to have a sample device to analyze, which isn’t our area of expertise.
This time, we won’t give it a name. It is not 100% clear what we are looking at, what are the exact characteristics of it, and how big this thing actually is. But there are some numbers, and where possible, we have made additional reconnaissance in order to better understand what we’re dealing with.
But let us first show you the data we’ve gathered, and leave conclusions closer to the end of this post.

Hello, everybody!
My name is Alexander Zubkov and today I’d like to talk about routing loops.
The third quarter of 2021 brought a massive upheaval in the scale and intensity of DDoS attacks worldwide.
It all led to September when together with Yandex, we uncovered one of the most devastating botnets since the Mirai and named it Meris, as it was held accountable for a series of attacks with a very high RPS rate. And as those attacks were aimed all over the world, our quarterly statistics also changed.
This quarter, we've also prepared for your consideration a slice of statistics on the application layer (L7) DDoS attacks. Without further ado, let us elaborate on the details of DDoS attacks statistics and BGP incidents for Q3, 2021.

Introduction
For the last five years, there have virtually been almost no global-scale application-layer attacks.
During this period, the industry has learned how to cope with the high bandwidth network layer attacks, including amplification-based ones. It does not mean that botnets are now harmless.
End of June 2021, Qrator Labs started to see signs of a new assaulting force on the Internet – a botnet of a new kind. That is a joint research we conducted together with Yandex to elaborate on the specifics of the DDoS attacks enabler emerging in almost real-time.
On implementing streaming algorithms, counting of events often occurs, where an event means something like a packet arrival or a connection establishment. Since the number of events is large, the available memory can become a bottleneck: an ordinary -bit counter allows to take into account no more than
events.
One way to handle a larger range of values using the same amount of memory would be approximate counting. This article provides an overview of the well-known Morris algorithm and some generalizations of it.
Another way to reduce the number of bits required for counting mass events is to use decay. We discuss such an approach here [3], and we are going to publish another blog post on this particular topic shortly.
In the beginning of this article, we analyse one straightforward probabilistic calculation algorithm and highlight its shortcomings (Section 2). Then (Section 3), we describe the algorithm proposed by Robert Morris in 1978 and indicate its most essential properties and advantages. For most non-trivial formulas and statements, the text contains our proofs, the demanding reader can find them in the inserts. In the following three sections, we outline valuable extensions of the classic algorithm: you can learn what Morris's counters and exponential decay have in common, how to improve the accuracy by sacrificing the maximum value, and how to handle weighted events efficiently.

The year 2021 started on such a high note for Qrator Labs: on January 19, our company celebrated its 10th anniversary. Shortly after, in February, our network mitigated quite an impressive 750 Gbps DDoS attack based on old and well known DNS amplification. Furthermore, there is a constant flow of BGP incidents; some are becoming global routing anomalies. We started reporting in our newly made Twitter account for Qrator.Radar.
Nevertheless, with the first quarter of the year being over, we can take a closer look at DDoS attacks statistics and BGP incidents for January - March 2021.

Why is it valuable to get into the Qrator Labs partnership program?
In Qrator Labs, we firmly believe that working together brings a better result. Which is the reason why, for years, we were trying to find meaningful partnerships with all kinds of companies. They either seek to provide their existing customers with the top-notch DDoS mitigation technology developed at Qrator Labs with many additional ecosystem solutions or want to succeed the other way around. By getting their product available for Qrator Labs' customers by integrating into the Qrator anycast filtering network.

By the beginning of 2021, Qrator Labs filtering network expands to 14 scrubbing centers and a total of 3 Tbps filtering bandwidth capacity, with the San Paolo scrubbing facility fully operational in early 2021;
New partner services fully integrated into Qrator Labs infrastructure and customer dashboard throughout 2020: SolidWall WAF and RuGeeks CDN;
Upgraded filtering logic allows Qrator Labs to serve even bigger infrastructures with full-scale cybersecurity protection and DDoS attacks mitigation;
The newest AMD processors are now widely used by Qrator Labs in packet processing.
DDoS attacks were on the rise during 2020, with the most relentless attacks described as short and overwhelmingly intensive.
However, BGP incidents were an area where it was evident that some change was and still is needed, as there was a significant amount of devastating hijacks and route leaks.
In 2020, we began providing our services in Singapore under a new partnership and opened a new scrubbing center in Dubai, where our fully functioning branch is staffed by the best professionals to serve local customers.

At the beginning of the year 2021, Qrator Labs is celebrating its 10 year anniversary. On January 19 our company marks the official passing of a formal 10 years longevity mark, entering its second decade of existence.
Everything started a little bit earlier - when at the age of 10 Alex saw the Robotron K 1820 - in 2008, when Alexander Lyamin - the founder and CEO of Qrator Labs, approached the Moscow State University superiors, where he worked as a NOC engineer at the time, with an idea of a DDoS-attack mitigation research project. The MSU's network was one of the largest in the country and, as we know now, it was the best place to hatch a future technology.
That time MSU administration agreed, and Mr Lyamin took his own hardware to the university, simultaneously gathering a team. In two years, by summer 2010, the project turned out to be that successful. It courted the DDoS attack of a bandwidth exceeding the MSU's upstream bandwidth capability. And on June 22 MSU superiors gave Mr Lyamin a choice - to shut down or find money to incorporate.
Alexander Lyamin chose to incorporate with his own means, which effectively meant that the needed infrastructure must be built from scratch. The initial design should be distributed instead of concentrated within one network, which resources were not enough for this specific task. And by September 1, 2010, those first server sites were ready and running.
This is a transcription of a talk that was presented at CSNOG 2020 — video is at the end of the page