In the DevOps realm, where automation is crucial, the management of resources and updating processes in the cloud is vitally important. Many modern projects, particularly in AWS cloud environments, leverage Auto Scaling Groups (ASG). This mechanism aims to achieve three key objectives: balancing loads, increasing service reliability, and optimizing operational costs for efficiency and effectiveness.
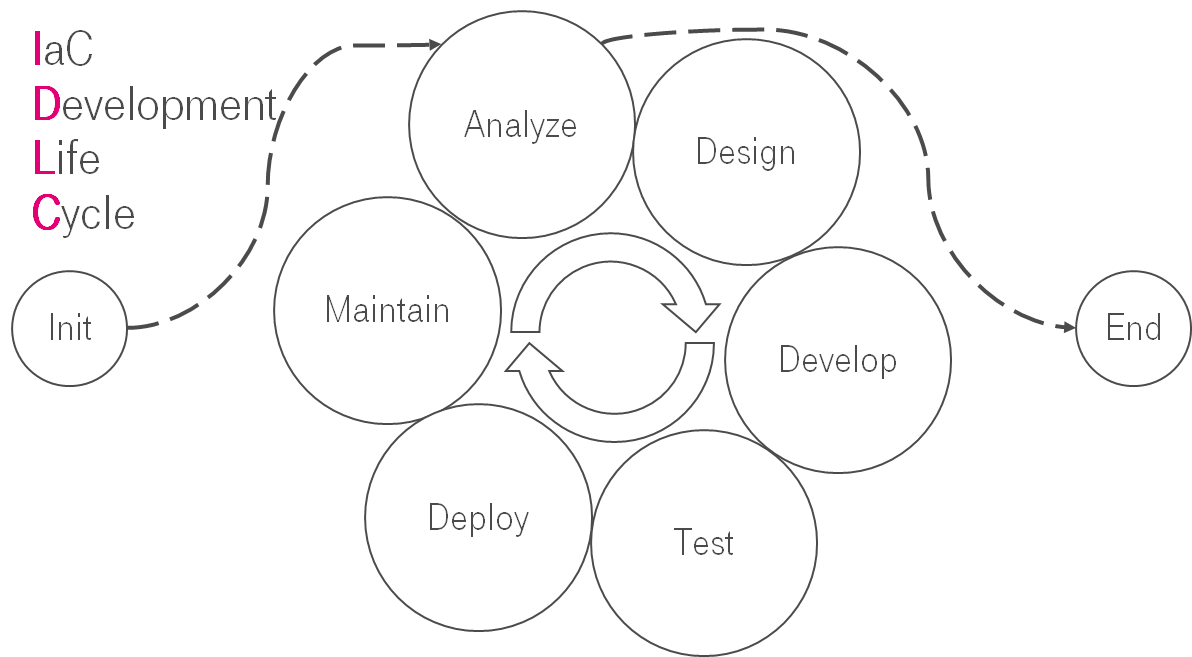
Imagine working at a company where you deploy applications on Amazon's resources. To streamline this process and manage configurations more effectively, you use pre-built AMI images. These are crafted with tools like HashiCorp Packer, ensuring your applications launch swiftly and reliably. For the actual infrastructure deployment, you turn to Terraform. It's widely recognized as the standard in many major companies for managing cloud resources and using the IaC (Infrastructure as Code) approach.
As an IT engineer, you sometimes need to update instance versions to a newer AMI image, either for the latest security patches or to introduce new functionalities. The challenge lies in updating an active ASG without causing downtime. It's crucial to ensure the new AMI performs as reliably as the existing one, balancing the need for updates with system stability and uptime.
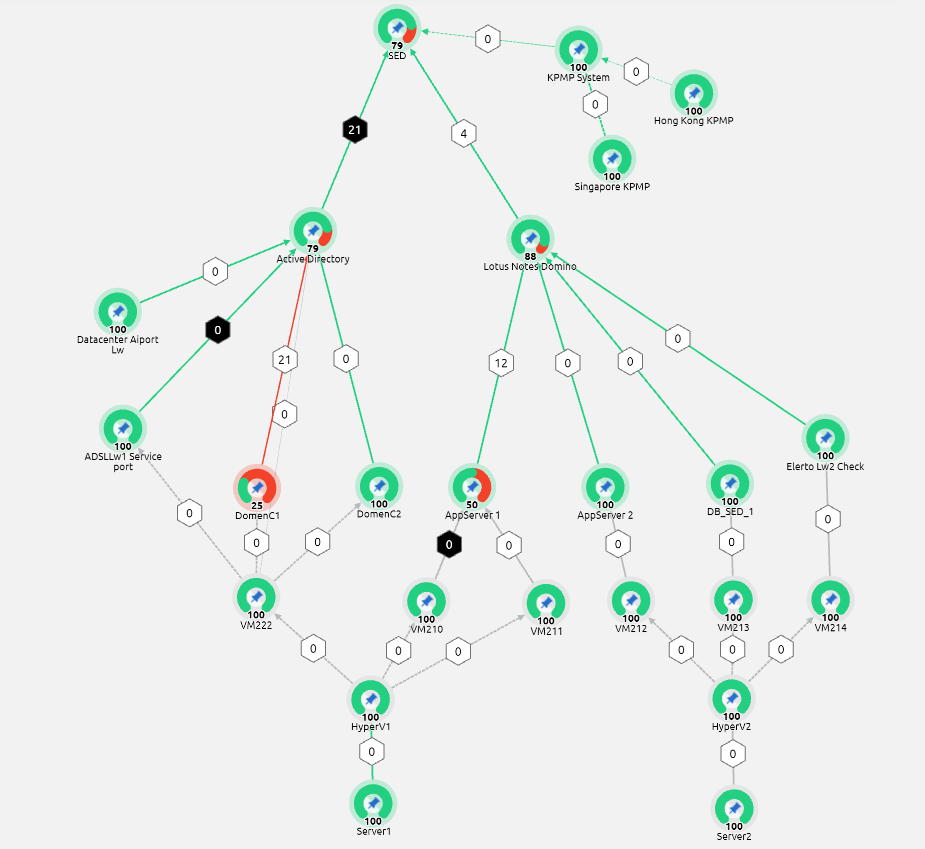
ASG's instance refresh is a crucial feature that allows for updating instances within a group while minimizing downtime, thereby maintaining high availability. However, ensuring the success of such updates, especially in large, complex systems, can be a challenge. Terraform resources, such as aws_autoscaling_group, can initiate this process but don't provide progress tracking. This limitation becomes apparent when other infrastructure components, such as certificate renewals or DNS updates, depend on the state and version of the instances. Monitoring the update process is essential to maintain an accurate infrastructure state after Terraform's execution.
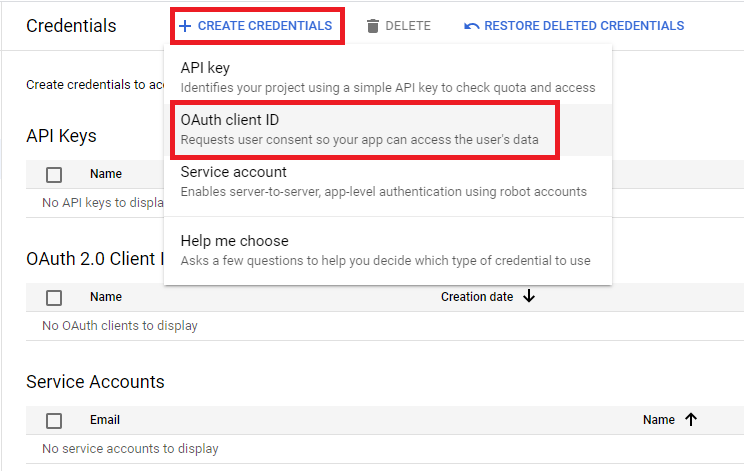
To overcome this challenge, Ansible can be utilized...