Guide to G
Introduction: Currently, many companies use H5 frameworks for app development, and among these H5 frameworks, uniapp is the most mature. Therefore, hbuilderx has become the preferred choice for developers. However, packaging an app requires a certificate. So how do we obtain this certificate? Generating an Apple certificate is relatively complex, so here I will focus on the process of generating an iOS certificate.
Currently, many companies use H5 frameworks for app development, and among these H5 frameworks, uniapp is the most mature. Therefore, hbuilderx has become the preferred choice for developers. However, packaging an app requires a certificate. So how do we obtain this certificate?
Generating an Apple certificate is relatively complex, so here I will focus on the process of generating an iOS certificate:
If you don’t have an Apple Developer account yet, you need to register for one in the Apple Developer Center. The tutorial for registering an Apple Developer account is as follows: Tutorial for Registering an Apple Developer Account (in Chinese).
Once you have the Apple Developer account, you can follow the steps below to create the certificate.
First, let’s create a p12 certificate. The process for creating a p12 certificate is as follows:
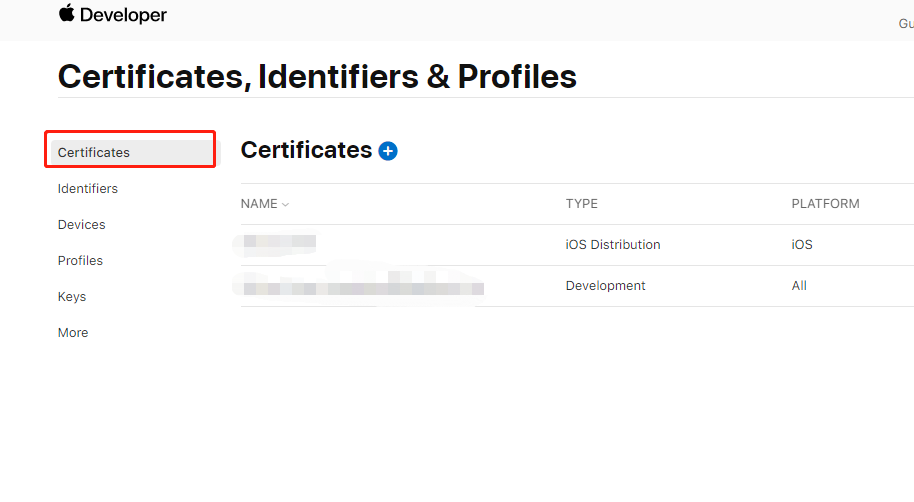
1.Log in to the Apple Developer backend and click on the “certificates” menu to enter the certificate management page. Click on the blue plus sign on the right side to start creating a certificate. When creating the certificate, choose the “iOS Distribution Ad Hoc and App Store” type, which includes both real device testing and distribution types (ad hoc for testing, app store for distribution). Please do not choose the “Apple” or “Dev” types of certificates, as they cannot be used for cloud packaging in hbuilderx.
2.During the creation of the certificate, it will ask us to provide a csr file, as shown in the image.
3.Switch to Appuploader.
Appuploader home — A tool improve iOS development efficiency such as submitting IPA to App Store and managing iOS certificates.
Use the function of generating iOS certificates in Appuploader to create this .p12 file, as shown in the image. After generating the .p12 file, download it to your local computer.
Go back to the Apple Developer Center. The .p12 certificate generated by appuploader will be synchronized back. You can then use appuploader to generate the p12 format Apple certificate.
With the above steps, the p12 packing certificate has been generated.
Now, let me teach you how to generate the profile file required for packaging:
1.Enter the Apple Developer Center and click on “Identifiers” to create an app ID (package name). After creating it, it should look like the image below. Note that the format of the package name is typically in the format of a Java package name: com.xxxxxx.yyy.
2.If you have already created the app ID from the previous step, you can then enter the “profiles” menu to start creating the profile file.
3.When creating the profile file, choose “