DENUVO Hypervisor. How does it work?

Analyzing a Denuvo bypass approach based on virtualization (Resident Evil: Requiem).
This article serves more or so to analyze this bypass approach and how to circumvent it on Denuvo’s side.

Disassemble and understand how it works

Analyzing a Denuvo bypass approach based on virtualization (Resident Evil: Requiem).
This article serves more or so to analyze this bypass approach and how to circumvent it on Denuvo’s side.

rexglue (https://habr.com/ru/articles/1002640/
example project with dolphin https://github.com/rexglue/demo-iruka
Replace with our .xex file (project), then start codegen

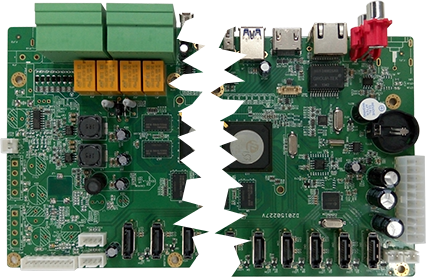
Hey, Habr! Ivan Glinkin is here again, head of the hardware research group from the Bastion team.
"A flash drive with a combination lock," "a flash drive with hardware encryption," "an encrypted USB drive," and finally, the proper term — "Cryptographic Module". An encrypted USB flash drive goes by many names, but the core concept remains the same.
The purpose of such a device is to protect sensitive information from unauthorized access at both the software and hardware levels through encryption, anti-tampering mechanisms, and various other safeguards. But are these secure USB drives really as reliable as they're made out to be, or is it all just smoke and mirrors?
We decided to look past the marketing claims and conduct our own investigation, attempting to crack several of these devices using hardware reverse engineering. We attempted to extract data, identify the encryption algorithms used, physically open the drives, and read their memory chips.
The results were quite interesting. Read on for the details.

Build the project as follows:
This command is for downloading from GitHub: https://github.com/rexglue/rexglue-sdk
Warning: You can download a pre-built .exe file, which will allow you to decompile the game in C++ (but building it is unlikely). Furthermore, versions are updated frequently, and the latest versions (with more instructions) are worth building.
Prepare the necessary directory.
Specify it as REXSDK in the global variables.
Sometimes the project won't compile in x64, so it's worth adding these lines to CMakeList.txt.
Enable Windows developer mode to download the necessary packages.
And in the /thirdparty/libsmpack folder, enter the following commands.
Then the necessary updates for the package will be downloaded.
Try adding additional parameters here. If it doesn't compile, then:
And finish the build:
Testing
To test the tool, use the following commands:
Add it to the assets/default.xex folder (you'll need to create it and add it to the project that rexglue will create).
This video can be useful for installing clang-cl and preparing default.xex from an Xbox 360 ISO image (which was dumped).
The program will display all missing instructions and replace them with placeholders (but it's best to create an issue with the required instructions, and once they're implemented, return to the project).
Don't forget to support the developers with well-deserved stars and share with your friends. Also, subscribe so you don't miss the next part, which will explain how to run the recompiled project.


Imagine someone withdrew money from a company's account at night. The next morning panic breaks out, leading to yet more problems. The IT department can reinstall a compromised system from scratch or restore it from backup. Reinstalling from scratch will wipe out all traces left by the attackers, and external investigators will have to search for clues in other systems. Restoring from backup carries the risk of accidentally reinstating a compromised image. In this paper, we will describe common mistakes that experts make when responding to security incidents.
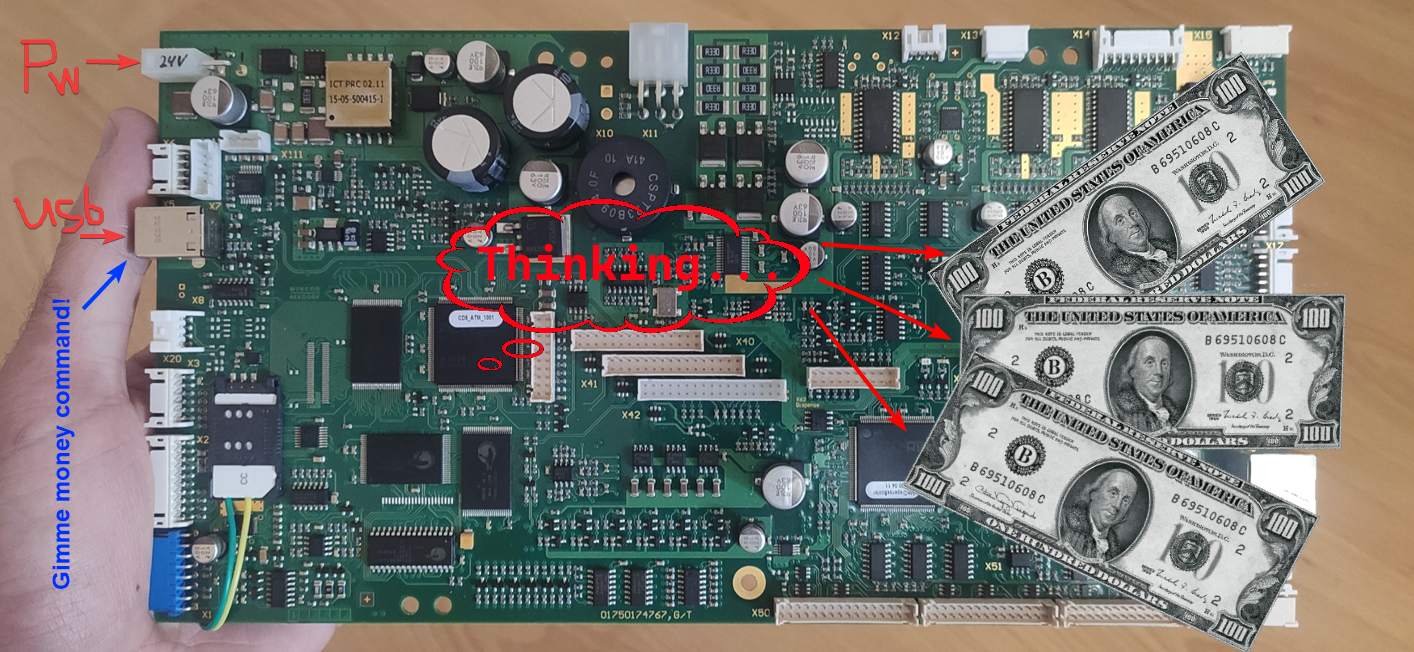
Hi there! A while ago, Positive Technologies published the news that ATMs manufactured by Diebold Nixdorf (previously known as Wincor), or more specifically, the RM3 and CMDv5 cash dispensers, contained a vulnerability which allowed attackers to withdraw cash and upload modified (vulnerable) firmware. And since my former colleague Alexei Stennikov and I were directly involved in finding this vulnerability, I would like to share some details.
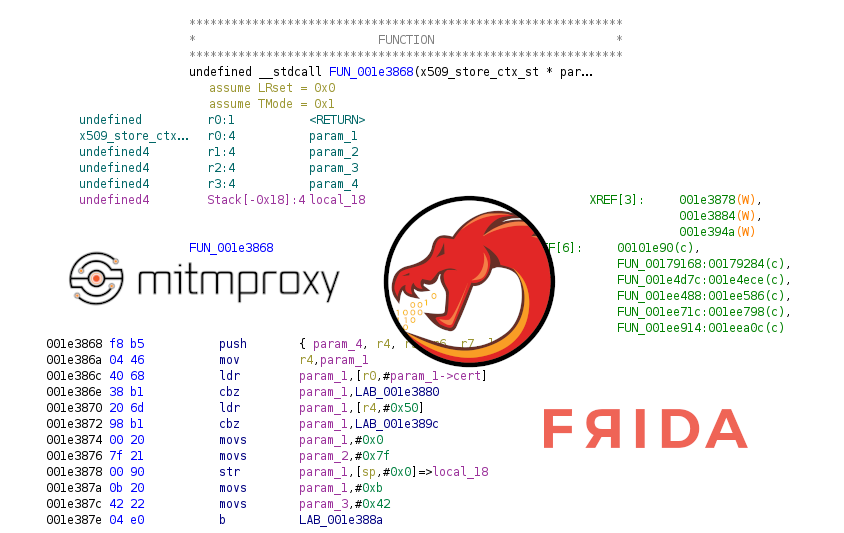
Once I was asked to save a traffic dump of an Instagram app while viewing one particular user profile. Simply saving the traffic dump on the router didn't make sense because the app used TLS to communicate with the server. Existing solutions didn't work because they worked with an older version of Instagram.
Below I will describe how I managed to do it myself using mitmproxy, ghidra and frida.

GDB is THE debugger for Linux programs. It’s super powerful. But its user-friendliness or lack thereof can actually make you throw your PC out of the window. But what’s important to understand about GDB is that GDB is not simply a tool, it’s a debugging framework for you to build upon. In this article, I’m gonna walk you through GDB setup for reverse engineering and show you all of the necessary commands and shortcuts for your debugging workflow.
Reverse engineering might seem so complex, that not everyone has the bravery required to tackle it. But is it really that hard? Today we are gonna dive into the process of learning how to reverse engineer.
First of all, try to answer yourself, what are you hoping to achieve with reverse engineering? Because reverse engineering is a tool. And you should choose the right tool for your task. So when reverse engineering might be useful?

Most likely you've already heard about the famous exploit checkm8, which uses an unfixable vulnerability in the BootROM of most iDevices, including iPhone X. In this article, we'll provide a technical analysis of this exploit and figure out what causes the vulnerability.

 Google loves easter eggs. It loves them so much, in fact, that you could find them in virtually every product of theirs. The tradition of Android easter eggs began in the very earliest versions of the OS (I think everyone there knows what happens when you go into the general settings and tap the version number a few times).
Google loves easter eggs. It loves them so much, in fact, that you could find them in virtually every product of theirs. The tradition of Android easter eggs began in the very earliest versions of the OS (I think everyone there knows what happens when you go into the general settings and tap the version number a few times).

Good day to you! 
My name is Stanislav and I like to write code. This is my first english article on Habr which I made due to several reasons:
This article is an english version of my very first article on russian.
Let me introduce the main figures in this story who actually fixed the bug preventing Git from running in ReactOS — the French developer Hermès Bélusca-Maïto (or just Hermes with hbelusca nickname) and of course me (with x86corez nickname).
The story begins with the following messages from the ReactOS Development IRC channel:
Jun 03 18:52:56 <hbelusca> Anybody want to work on some small problem? If so, can someone figure out why this problem https://jira.reactos.org/browse/CORE-12931 happens on ReactOS? :D
Jun 03 18:53:13 <hbelusca> That would help having a good ROS self-hosting system with git support.
Jun 03 18:53:34 <hbelusca> (the git assertion part only).