
At Altenar, we often use RabbitMQ as an entry point for our products. How to protect the TCP load balancer with a ManagedSSL certificate is described further.

SSH (Secure Shell) is the backbone of remote system administration and secure remote access, serving millions of developers and system administrators daily. However, when SSH connections fail, the cryptographic nature of the protocol can make debugging challenging. The complex interplay between authentication mechanisms, encryption algorithms, and network layers often obscures the root cause of connection issues. This complexity is further compounded by the protocol's security-first design, where error messages are intentionally vague to prevent potential attackers from gathering system information. Whether we're dealing with key authentication failures, network connectivity issues, or configuration mismatches, understanding the underlying SSH architecture becomes critical for effective troubleshooting.

In today's interconnected development world, secure authentication is not just a luxury—it's a necessity. Whether you're a seasoned DevOps engineer or a junior developer just starting your journey, understanding SSH key pairs is crucial for your daily workflow. They're the unsung heroes that keep our git pushes secure, our server access protected, and our deployments safe from prying eyes.
But let's be honest: SSH keys canbe confusing. With terms like “public key infrastructure,” “cryptographic algorithms,” and “key fingerprints” floating around, it's easy to feel overwhelmed. This guide aims to demystify SSH key pairs, breaking down complex concepts into digestible pieces that will help you make informed decisions about your security setup.

CAPTCHA is not just a single word that can be defined; it's an acronym consisting of nine words (and two prepositions): Completely Automated Public Turing Test To Tell Computers and Humans Apart. This mouthful was shortened to the concise CAPTCHA to avoid creating yet another hard-to-pronounce term. Translated into Russian, this abbreviation sounds like "Полностью автоматизированный публичный тест Тьюринга для различения компьютеров и людей" (Fully Automated Public Turing Test to Differentiate Computers and Humans).

Recently I have bought starfive visionfive-2 SoC for my own experiments, honestly speaking
I am striving to work with risc-v. After some time I decided to share my experience. Here my bulletpoints:
Small preparation USB-to-Serial connector Write image to microSD/SSD Set boot mode settings
Boot Update bootloader Build kernel Native build Pod build Cross-build on amd64: fast and handy
Chroot to risc-v system from amd64 and install packages
Bonus 1: run qemu with risc-v
Bonus 2: build deb packages for risc-v
Bonus 3: kernel build script
Conclusions

Kata Containers is actually now the main way to run containers in an isolated virtual machine for greater security. I tell you how to install them for use with Containerd and Docker while still being able to switch between release versions.

A story about evolving our CI process for a monolithic Python repo with tests, challenges faced, and solutions. Discussing Docker, linters, Allure TestOps, and more.

Today, a significant portion of all content on the Internet is distributed with the use of CDNs (Content Delivery Networks). At the same time, there is no research on how various censors extend their influence on such networks. Scientists from the University of Massachusetts analyzed possible methods of blocking CDN content using the example of the practices of the Chinese authorities, and also developed a tool to bypass such blocks.
We (specialists from proxy service) have prepared an overview material with the main conclusions and results of this experiment (translate of this material).

In this tutorial, I’ll show you how to deploy a full-stack JavaScript web app into Firebase. We’ll deploy a Next.js application to Firebase hosting. I’ll show you a quick and efficient process that can be completed in 5 minutes.

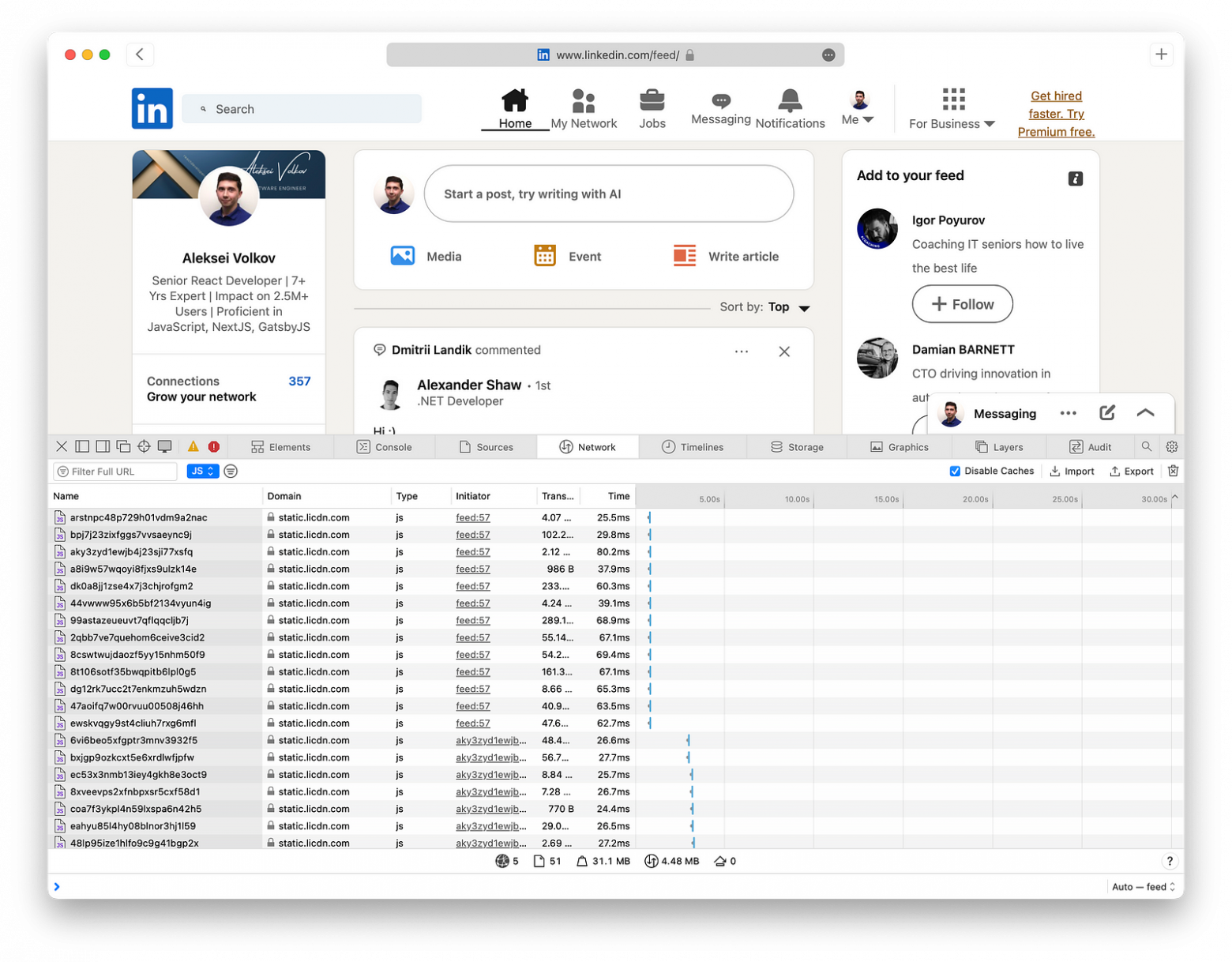
We are requesting 20,000,000 euro to place 900 orders on the exchange. What could go wrong?
Today, I will explain how to avoid losing billions in client money when executing large transactions on the exchange. This discussion focuses on an often overlooked and largely invisible problem that arises when handling large requests, particularly HTTP requests, which may not be fully executed. It's surprising how little attention is given to this issue and how few tools there are to address it.
Our task was to implement large-scale management of exchange orders, not just within a single exchange but globally, and to ensure it operates reliably. In this story, you'll encounter clients, servers, and cats. Stories are always more enjoyable with cats.

In the world of IT services, the idea that operations must run 24/7 is often taken for granted. However, for business-to-business (B2B) services, this assumption needs to be rethought. By reconsidering the need for around-the-clock processing services, companies can achieve significant benefits in efficiency, security, and sustainability.

Governments in many countries restrict citizens' access to information and services on the Internet in one way or another. Combating such censorship is an important and difficult task. Usually simple solutions cannot boast about high reliability or long-term efficiency. More complex methods of overcoming blocks have disadvantages in terms of usability, low performance, or they do not allow you to maintain the quality of Internet use at the proper level.
A group of American scientists from the University of Illinois has developed a new method of overcoming blocks, which is based on the use of proxy technology, as well as segmenting users by trust level to effectively identify agents working for censors. We present you with the main theses of this work.
Description of the approach
Scientists have developed the Salmon tool, a system of proxy servers operated by volunteers from countries without restrictions on Internet use. In order to protect these servers from blocking by censors, the system uses a special algorithm for assigning a level of trust to users.
The method involves exposing potential censor agents that pose as ordinary users in order to find out the IP address of the proxy server and block it. In addition, countering Sybil attacks is carried out through the requirements to provide a link to a valid social network account when registering in the system or to receive a recommendation from a user with a high level of trust.
How it works
It is assumed that the censor is a state–controlled body that has the ability to take control of any router within the country. It is also assumed that the task of the censor is to block access to certain resources, and not to identify users for further arrests. The system cannot prevent such a course of events in any way – the state has plenty of opportunities to find out what services citizens use. One of them is the use of honeypot servers to intercept communications.
It is also assumed that the state has significant resources, including human ones. The censor can solve tasks that require hundreds and thousands of full-time employees.
A few more basic theses:

Wearable Digital Health Technologies for Monitoring in Cardiovascular Medicine
This review article presents a three-part true-life clinical vignette that illustrates how digital health technology can aid providers caring for patients with cardiovascular disease. Specific information that would identify real patients has been removed or altered. Each vignette is followed by a discussion of how these methods were used in the care of the patient.

Masking an IP address with a use of a proxy is necessary not only to circumvent censorship on the Internet and watch TV series. In recent years, proxies have been increasingly used to solve corporate objectives from application testing under load to competitive intelligence. Habr has a good overview of the various options for using proxies in the business sector.
Today we will talk about what to pay attention to when choosing a proxy network for solving such corporate objectives.

IP address masking may be required for various tasks – from accessing blocked content to bypassing anti-bot systems of search engines and other online resources. We found an interesting post about how this technology can be used to solve corporate objectives.
There are several options of implementing a proxy:

Hi Everyone.
Recently I got Asus E200H laptop, which I would like to use as a portable computer to work with a high-precision equipment.
Within the scope of the article we will perform the experiment about the upgrade of the default 32 GB eMMC capacitor to 256 GB and will test it.
Have a nice reading!

Internet censorship is becoming an increasingly important issue worldwide. This leads to increasing of the "race of armaments" – in different countries government agencies and private corporations try to block various content and fight against the ways of circumventing of such restrictions. At the same time developers and researchers strive to create effective tools to combat censorship.
Scientists from Carnegie Mellon University, Stanford University, and SRI International conducted an experiment in which they developed a special service for masking the use of Tor – one of the most popular tools for bypassing blocking. Here is the story about the work done by the researchers.
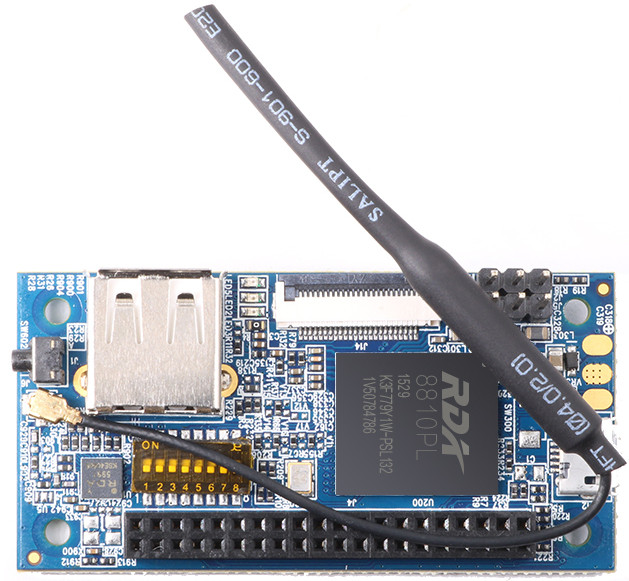
Hello my name is Dmitry. Recently I wrote article "Building firmware for Orange PI i96 (Orange PI 2g-iot) from scratch" . If you haven't read it yat, I highly recommend. And there I noticed that in order to build firware on current kernel, I have to rewrite drivers wirh new archetecture "Device tree". In this article I have revelate how I do it.
In the internet’s early days, blogging was straightforward. A server with PHP and MySQL allowed you to share your thoughts globally. Even FTP access with an index.html file sufficed.
However, as the web evolved, so did blogging requirements. Non-programmers needed user-friendly web interfaces, faster loading times, and seamless daily publishing. Platforms like Reddit, WordPress, and Tumblr emerged, but they faced a common issue: website ownership.