Cars are among the most technologically advanced consumer-level devices on the market. They have been shaping lifestyles, laws, supply chains, and many other aspects of human society's evolution.
But today, we’re witnessing a silent revolution – one driven not by hardware, but by software. Modern cars are no longer just machines; they’re dynamic, evolving platforms powered by code. This transformation is reshaping every aspect of the automotive industry, from design and manufacturing to ownership and recycling.
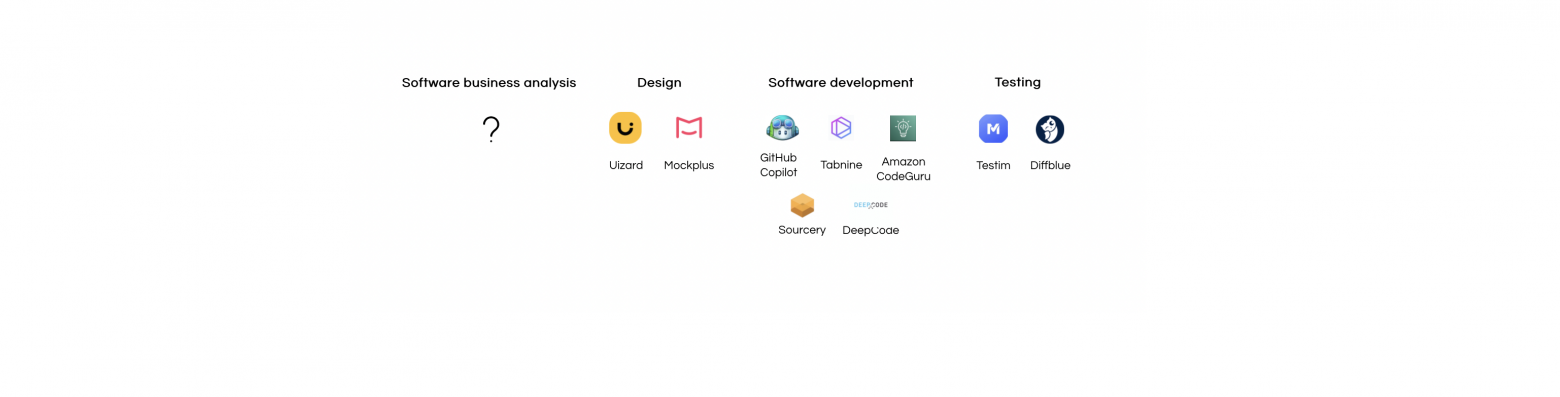
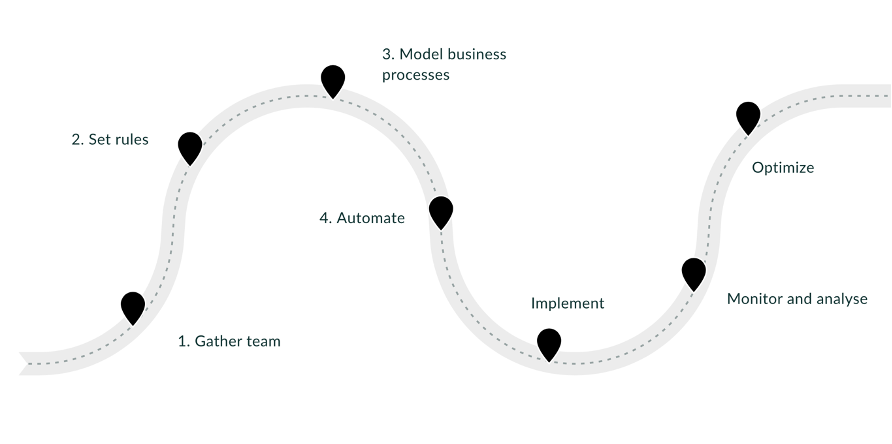
In my latest article, I explore six levels of evolution brought about by software’s growing role in vehicles and related fields:
Capabilities - Over-the-air updates and digital twins unlock new features and extend hardware lifespans.
Design - Digital platforms replace manual processes, enabling faster innovation.
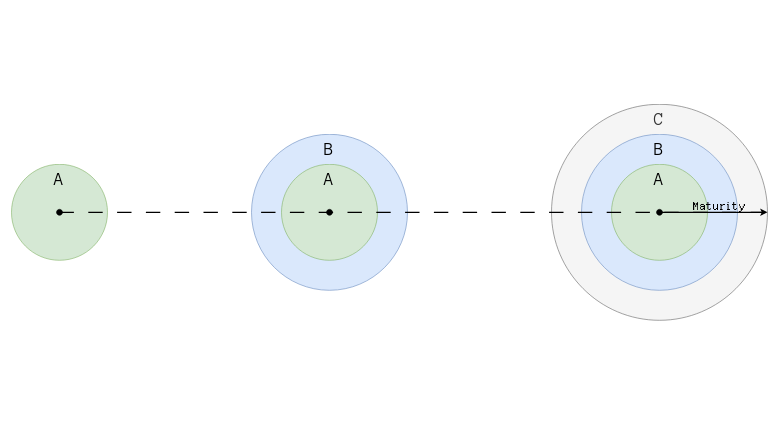
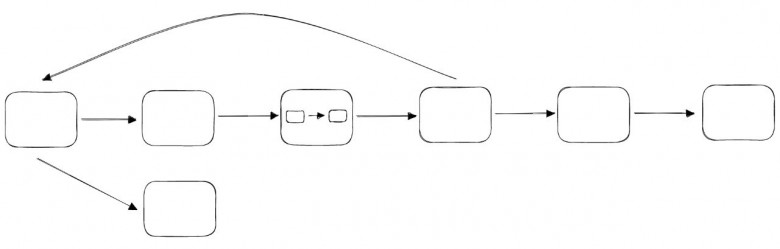
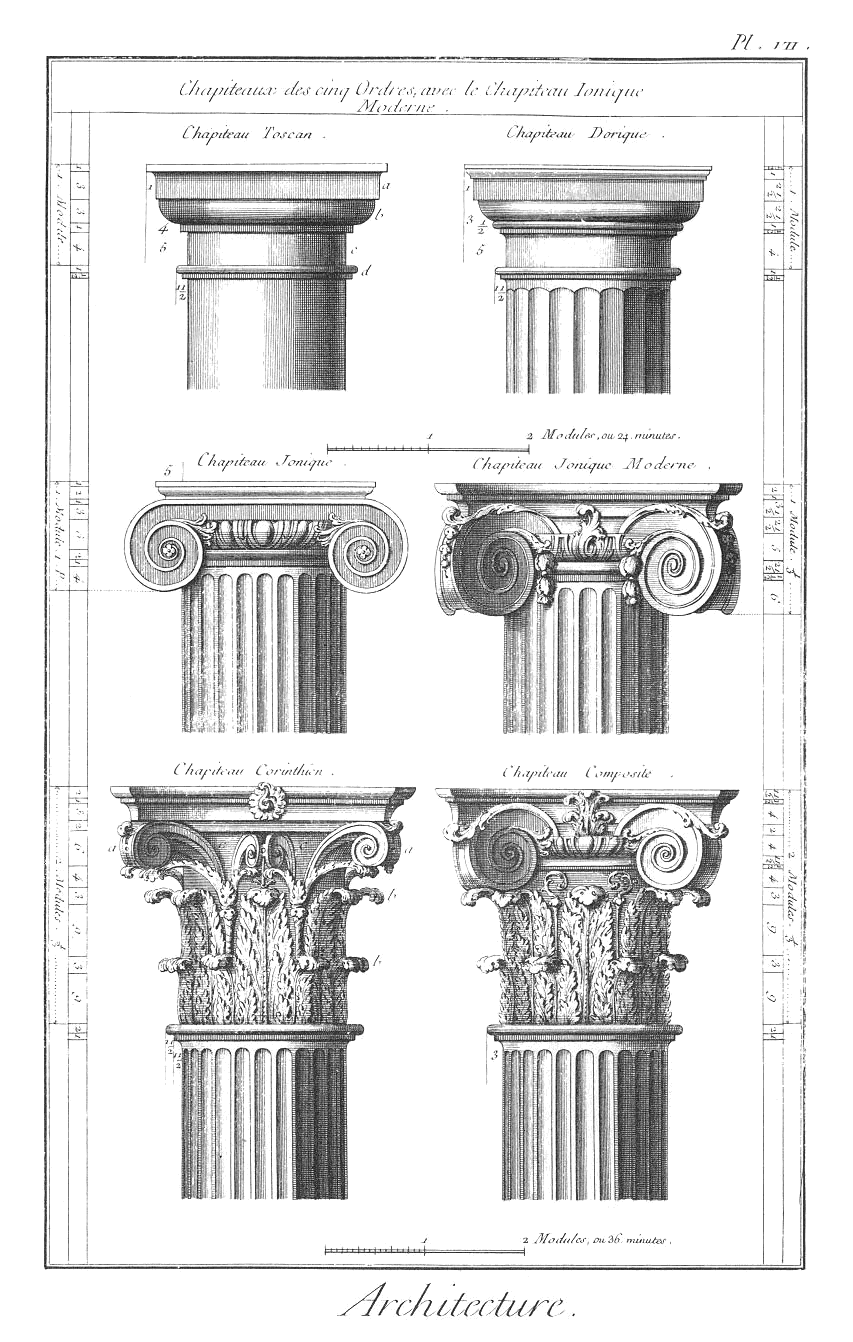
Architecture - Modular systems open doors to new partnerships and revenue streams.
Engineering - Agile, feature-centric paradigms align hardware and software development.
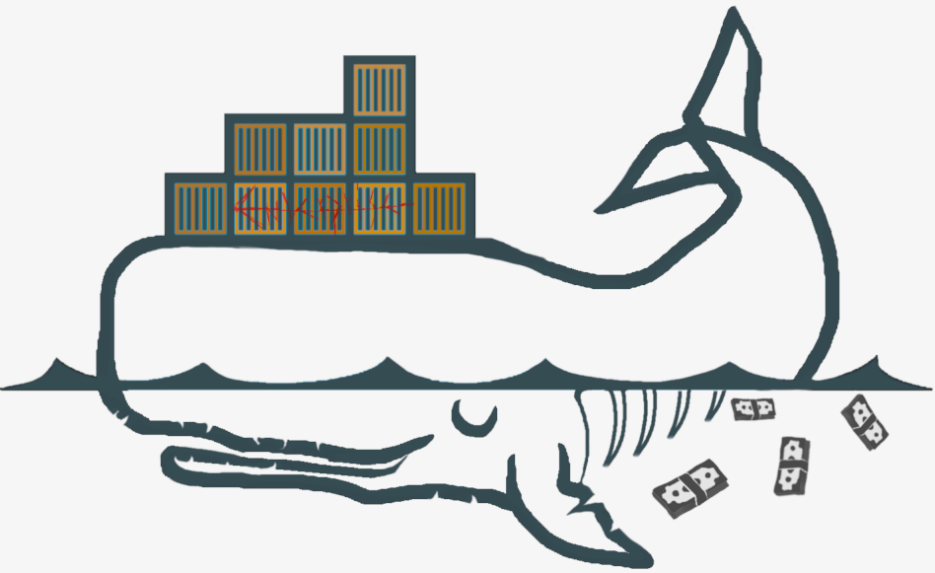
Manufacturing - Factories become dynamic, software-driven ecosystems for flexibility and sustainability.
Lifecycle - Software extends vehicle lifecycles, from supply chains to closed-loop recycling.
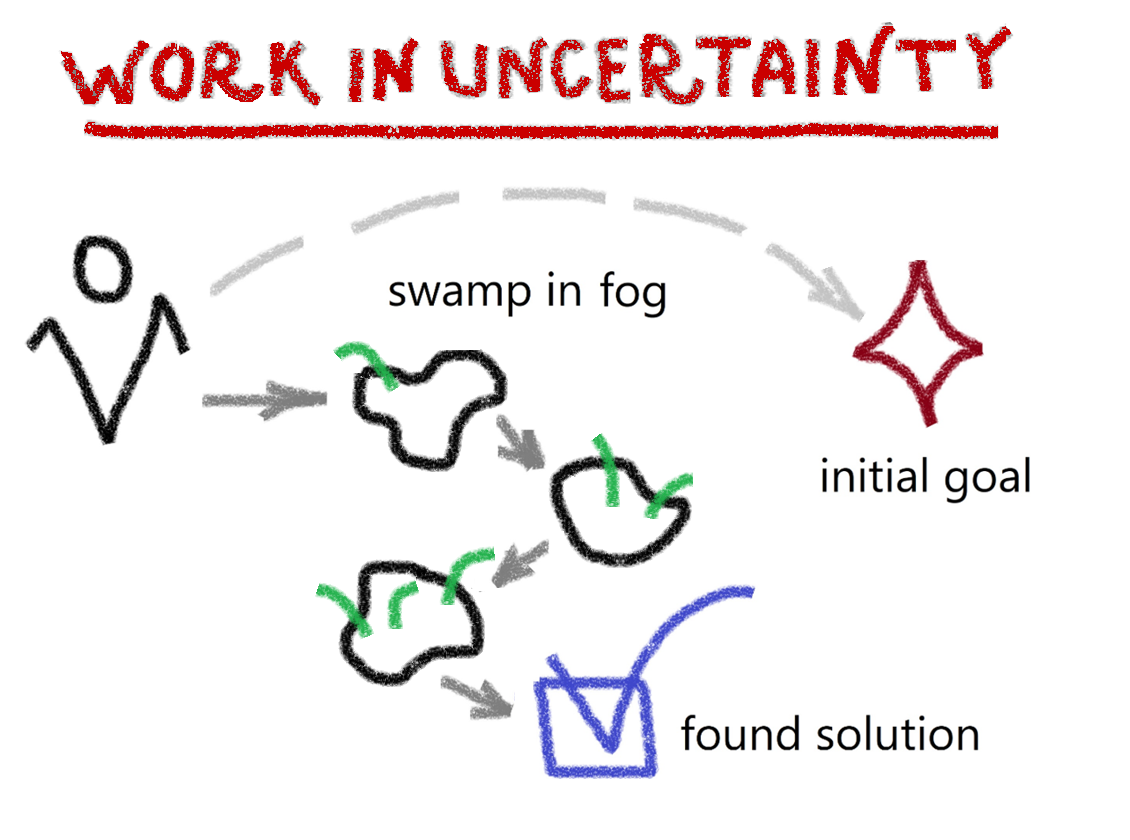
This transformation isn’t just about technology – it’s about reimagining the industry itself. Do we need a revolution to achieve a better, more sustainable future, or do we already have the tools to evolve?
The automotive industry is at a crossroads. For engineers, it demands fluency in code. For industries, it requires agility. For the planet, it offers a roadmap to reconcile mobility with sustainability.
The road ahead is coded, but the destination is open-ended – shaped by collaboration, innovation, and the choices we make today.