Corporations that dominate the market can impose their conditions on customers. This is also the case with everyone's favorite Netflix. When you make good content and you are sure that your audience wants to consume your content, you can start to increase the subscription price gradually. But the distribution of subscription costs around the world is unequal. This happens not only with Netflix, it happens with many big corporations: Microsoft, Sony, etc.
Naturally, everyone wants to watch high-quality content, but no one wants to overpay for it. And that led to creation of different schemes, for example, the one I'm going to describe here.
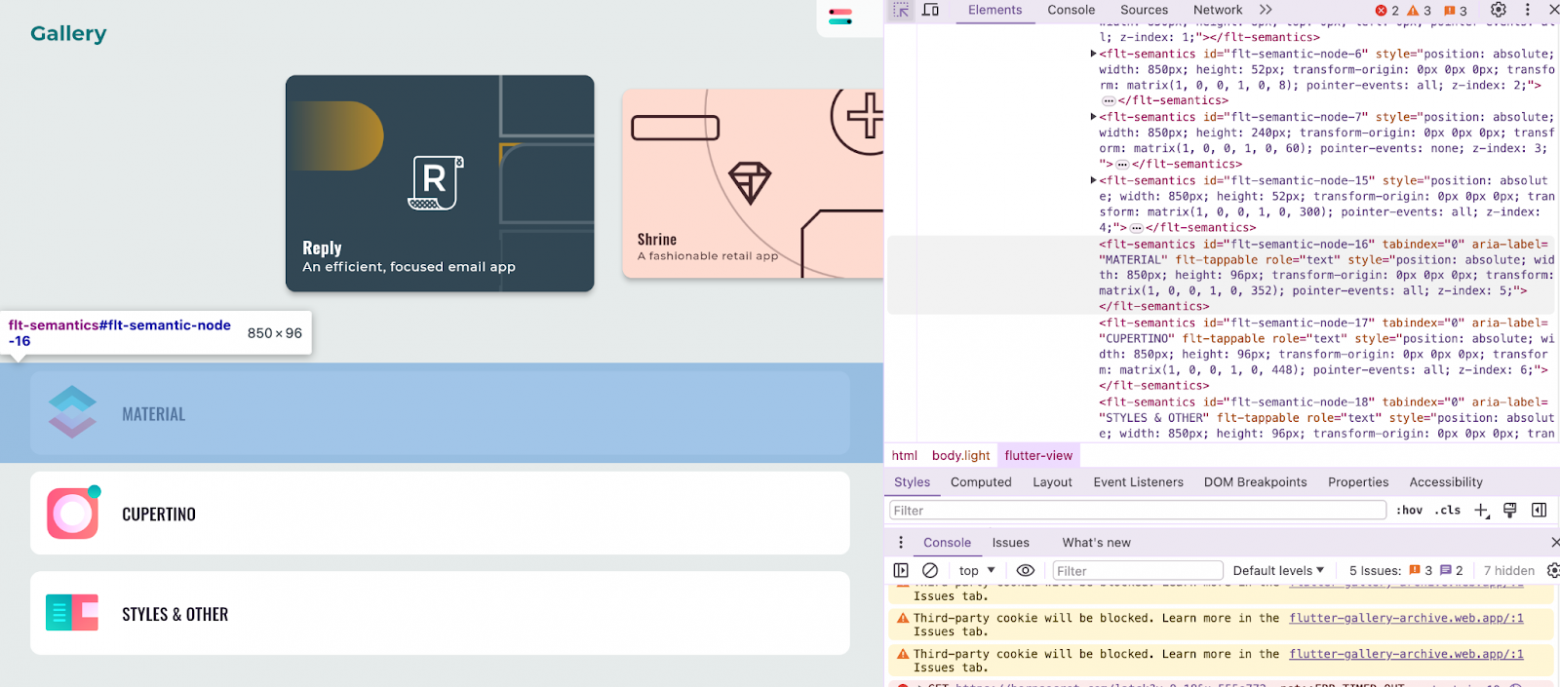
The essence of the scheme is simple – you buy a subscription for another region while staying in your home region. Of course, you can do this, but before I describe the scheme in detail, you should understand that Netflix is not as simple as it seems. When buying a subscription, for example, as a user from Pakistan, you should know that only the content that is allowed in that country will be available to you. Meaning, any sign of eroticism in movies, for example, is forbidden there.
And now this scheme appears in a completely opposite light. You can use my scheme if you want to access content that is blocked in your country, but you need to be prepared that the price will not be the same as for your region.
Top Three cheapest countries (in terms of the Netflix subscription price)