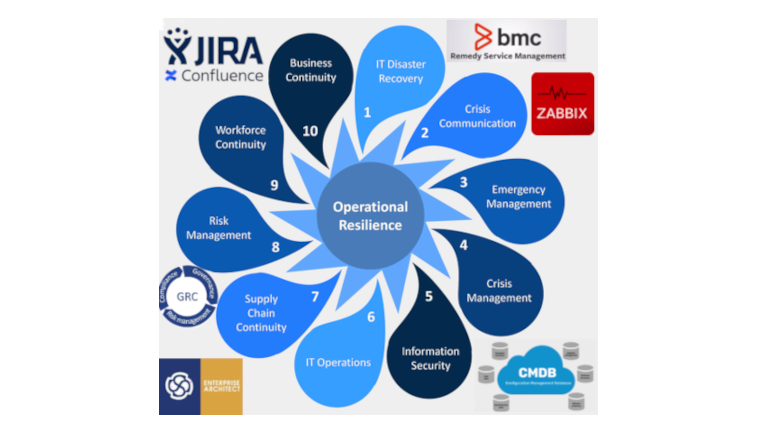
Recently, The BCI, one of the leading institutes working in the field of organizational resilience and business continuity, issued its regular report BCI Operational Resilience Report 2023 in collaboration with Riskonnect, who work with risk management solutions.
One of the questions they asked the respondents was if there was a difference between organizational resilience and operational resilience. As the answers demonstrated, for most respondents (and in most companies) these terms were used as synonyms. Having studied the report, the colleagues brought up another matter – The BCI introduced the new term of "organizational resilience" in addition to "business continuity" and "operational resilience".
If we search Habr for "Business Continuity", "DRP", "BCP", or "BIA", we’ll find quite enough posts by my colleagues (I’ve met some of them face to face and worked with the others) about data system recovery, data system testing, fault-tolerant infrastructure, and some other things. Yet, hardly any of them explain where all of it has come from, how it is changing, where it is heading – and why.
I thought the time has come to change the situation for the better and answer some of the questions like where business continuity provisions and operational resilience has come from, how they are changing, and where this trend is heading and why. To share my thoughts about development of the industry and its current de-facto state in case of a mature (or not too mature) introduction level – some things I’ve stated for my own use.